In-depth Analysis of a Newly Discovered MSI-Based Malware
Author: Nullsans and GPT
1. Malware Overview
- File Type: Windows Installer Package (.msi)
- Behavior: Silently drops malicious PE and DLL files into hidden locations such as AppData and Startup folders.
- Persistence: Creates .lnk shortcut files for auto-launch at system startup.
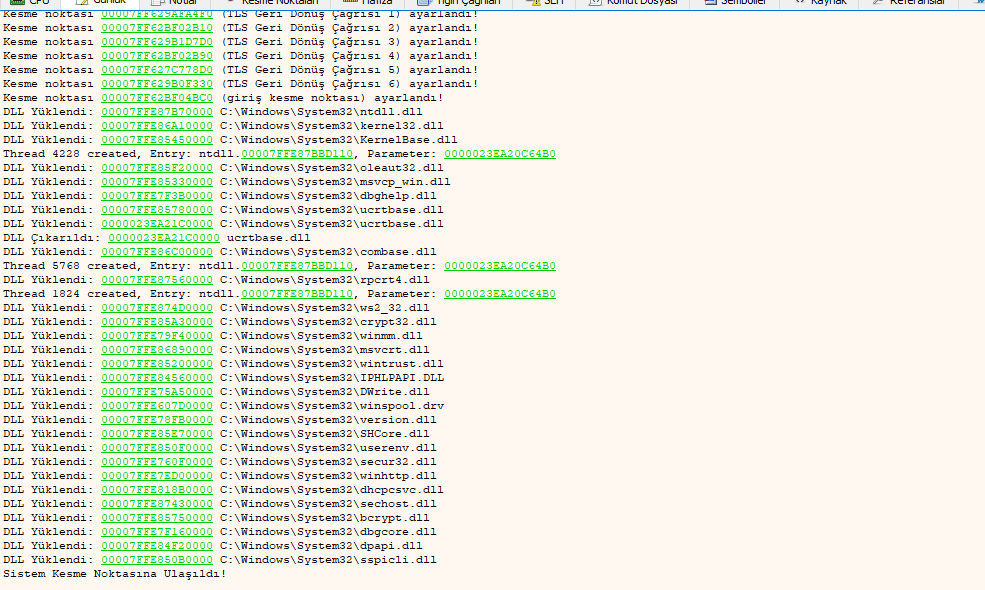
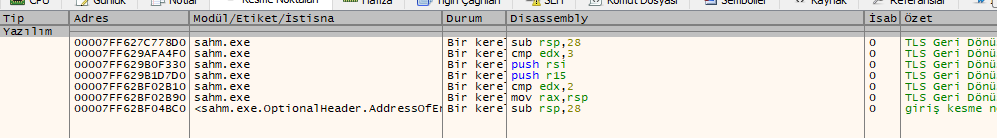
- Command & Control (C2): HTTP with TLS encryption.
- Architecture: Modular with helper DLLs and obfuscation.
2. Technical Operation
a) Installation & Propagation
- Copies itself to AppData during install.
- Drops PE and DLL payloads.
- Creates .lnk files for persistence.
b) System & API Usage
- Uses
CreateProcess,WriteProcessMemory,VirtualAlloc. - Modifies registry keys for startup execution.
- Loads PowerShell BitLocker module.
c) Network & C2
- Encrypted traffic over HTTP+TLS.
- Supports dynamic tasking and data exfiltration.
- Targets Chromium-based browsers for data theft.
d) Stealth & Obfuscation
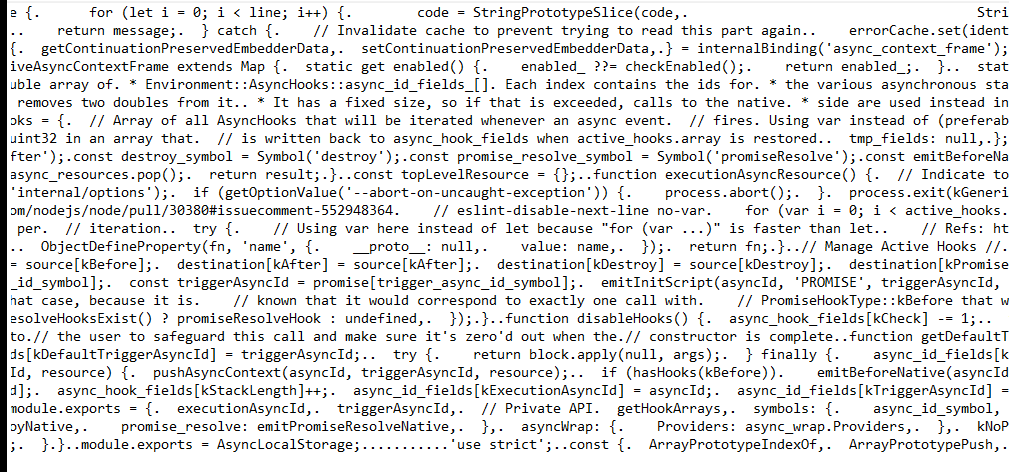
- Uses
async_hooksandasync_context_framefrom Node.js. - Custom PE sections to hinder analysis.
- Multi-layered obfuscation strategies.
3. Analysis Techniques
Static
- Inspect PE headers and import tables.
- Trace memory and process APIs.
- Review async_hooks structure.
Dynamic
- Use sandboxes and Process Monitor.
- Analyze TLS network traffic (Wireshark).
- Study dropped files in VM.
4. Defense Recommendations
- Don’t run unknown .msi installers.
- Use EDR with behavioral detection.
- Audit Startup folders and registry often.
- Flag encrypted outbound HTTP traffic.
- Harden PowerShell usage with policies.
- Block known hashes and IPs using IoCs.
5. Conclusion
This malware disguises itself as an innocent MSI installer, but beneath that surface, it employs advanced methods to persist, communicate secretly, and steal sensitive information. A multi-layered defense strategy is crucial to mitigate such threats.
6. Indicators of Compromise (IoCs)
- MSI Hash: 97707cb776e5028f0bbf676505e894a6
- Dropped Files: sahm.exe, DLL modules
- Shortcuts: .lnk files in Startup/Desktop
7. Analysis Images
If you have more findings or questions, feel free to reach out or contribute!